Looking at the state of Cybersecurity by news headlines, one would logically assume that ransomware is all security professionals must worry about in their day-to-day operations. The nemesis of the moment is Petya. Petya is a ransomware variant that is built on the chassis of a leaked National Security Agency exploit called Eternal Blue. The ransomware looks for unpatched Windows machines of all flavors running SMB 1.0.SMB stands for Server Message Block It’s an outmoded application layer file-sharing protocol that has been superseded by Active Directory and later versions of SMB. Petya encrypts your Master Boot Record, so that you can’t do anything while it works to encrypt the rest of your files. The result? You can either pay $300 in Bitcoin to some shadowy Russian hacking group and maybe get a decryption key for your files, or turn off SMB 1.0. To turn off SMB, you’ll need to navigate to your windows features setting, uncheck the offending service, and reboot.
But Ransomware isn’t the nightmare that should keep security professionals up at night. Indeed, a good backup policy mitigates any lapses in patch management. What should keep us up at night is our own state of being human. As humans, we are imperfect creatures. As much as we strive for greatness, there is always that one thing we might not have accomplished while juggling the many tasks of our daily rituals. Statistically, the vulnerabilities we see reflect the state of our profession.
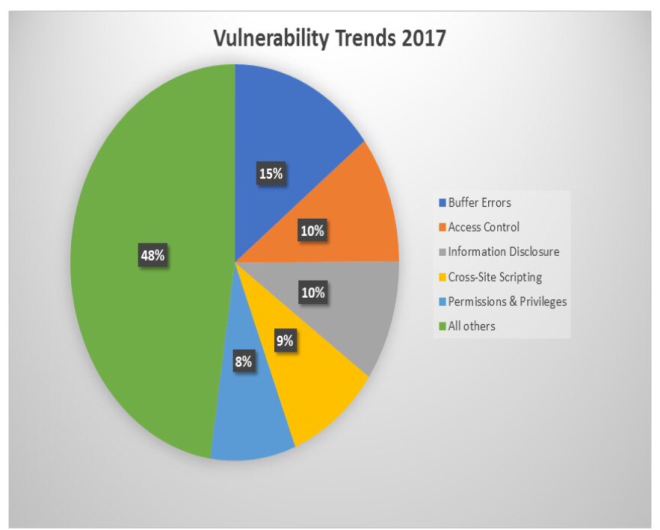
Per the National Institute of Standards and Technology (NIST) National Vulnerability Database (NVD), the greatest threat of 2017 isn’t Ransomware, it’s buffer-errors, followed by improper access controls, information leaks / disclosure, cross-site scripting, and permission, privileges and access control weaknesses.
Buffer-overflows? Okay, I get it. The development world is complex, and errors are going to happen. One of the beauties of our human condition is that we can always find better ways to do things, or, on the malevolent side, ways to exploit things. Luckily, protections against buffer-overflows are evolving using safe libraries, stack and executable containment strategies.
Cross-site scripting (XSS) has been on the security radar for a while now, yet it has declined from its height of 14.3% of all vulnerabilities in 2009, to its current 9.2%. XSS is a legitimate attack vector, and its decline in prevalence shows that developers and admins have been waging an effective battle against the threat. The industry focus on web threats has led to some interesting countermeasures, including containerization (essentially running a browser in its own virtual machine), JavaScript sandboxing, and Content Security Policies (CSP); all leading to effective mitigation of the threat.
What should give security folks pause, is the rise in threats that stab at the very heart of our job description. Ensuring the confidentiality, integrity, and availability of information resources is what we do for a living. On a personal level, each of us should take offense that vulnerabilities exploiting access controls, permissions, and privileges even exist, let alone rank among the top threats to our networks. To be sure, buffer-overflows can lead to escalation of privilege, but we must not assume that security faults in controls and privileges are solely the result of software weaknesses. Certainly, NIST doesn’t take this approach as they have made buffer-overflows its own category, separate from access and privilege threats.
So, what do we do? First and foremost, we should let go of our ego. Don’t assume that every security detail has been taken care of. Get in the habit of double-checking yourself, make sure those privileges and controls are properly set, and most important, still relevant. If security needs are not being met, double-down on ensuring your settings are up to date. Use those checklists, validate your templates, and adopt habits that put security first.
Let’s make it a community goal to not see security essentials on the NVD vulnerability trends for 2018.
